Global Site
Displaying present location in the site.
Ear Acoustic Authentication Technology: Using Sound to Identify the Distinctive Shape of the Ear Canal
Core Technologies and Advanced Technologies to Support BiometricsJust as each face has its own unique characteristics, so too do other parts of the head. The ear, for example, has many distinct features, including the shape of the ear canal. Ear acoustic authentication is a new biometric technology that identifies the shape of the ear canal using an earbud-type recognition device to measure reflected sound inside the ear. Authentication is possible at any time or place simply by having subjects listen to the sound. It is also possible even if the subjects are wearing gloves and masks. Combining this technology with hearables — emerging ear buds with advanced computing — makes possible a hands-free, eyes-free connection to AI, increasing the power of ICT to enhance human potential.
1. Introduction
Recent technologies use computer vision to capture and identify unique biological characteristics to more efficiently and accurately identify specific individuals, simultaneously providing more powerful security capability. However, one of the limitations of conventional biometric systems is that they require scanners and cameras capable of reading bio-information. As a result, they can typically only be used be access control at designated entrances and exits, or for surveillance. In situations where subjects are likely to be wearing gloves, masks, or other protective clothing, many of these systems will have difficulty performing accurate authentication. NEC’s ear acoustic authentication technology1) was developed to overcome these drawbacks. Because subjects have only to listen to the sound broadcast in their ears, anytime, anywhere authentication is possible, even if the subjects are wearing gloves and masks.
2. What Is Ear Acoustic authentication?
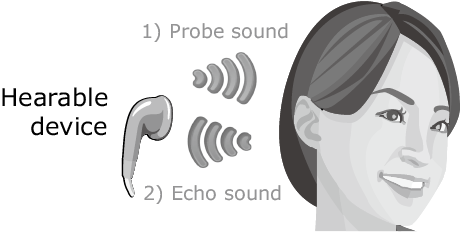
Just as each face has its own unique characteristics, so too is each head is distinguished by its own distinct features. NEC’s ear acoustic authentication system transmits as test sound via an earbud-type device as shown in Fig. 1 in the direction of the ear canal (external auditory canal). The reflected sound is measured to determine the specific shape of the ear canal. As the biodata is drawn directly from the living body, it is virtually impossible to falsify, giving this technique a tremendous advantage over other biometrics. This makes it easy to add a high security layer in environment where devices are commonly worn on or in the ears — such as when transceivers or wireless headsets with microphones are used, when earphones or headphones are used to listen to music, or when hearing aids are used.
The basic principles of ear acoustic authentication can be explained with the air column resonance you learn in high school physics. Air column resonance is the resonant frequency of sound waves that pass through a pipe filled with air. Air column resonance is the mechanism by which the flute and other wind instruments are able to generate particular sounds. The length of the ear canal is about 2 to 3 cm. Ear canal with ear buds can be regarded as closed-end air tube. The speed of sound is about 340 m/sec. The frequency of the first harmonic (fundamental tone) of the resonance is 5 to 7 kHz. Resonance is further generated in the frequencies of the harmonics — as in the second harmonic (10 to 14 kHz) and the third harmonic (15 to 21 kHz). The frequency at which the resonance occurs differs depending on the length of the ear canal. The strengths and attenuation of the resonance also vary according to differences in the shape of the ear canal and the hardness of the skin. For this reason, the distinctive shape of an individual’s ear canal can be extracted by transmitting a test sound that incorporates a wide range of frequencies and observing the sonic reflections. Fig. 2 shows the spectra of the reflected sounds measured on three different subjects. The positons of the peaks of the spectra represent the frequencies at which the resonance occurred while the heights of the peaks represent the strength of the resonance and the widths of the peaks represent the attenuation of the resonance.
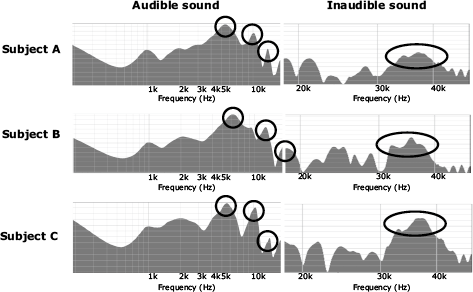
In addition, a recent study has found that resonance exists even with sound over 18 kHz which is inaudible to the human ear. This means that individuals can be identified using inaudible sounds2), making it possible to identify someone without interrupting their behavior and bothering their feeling.
3. Ear Acoustic Authentication and Hearables
Ear acoustic authentication is ideally suited for use with hearables — electronic in-ear devices that have become increasingly common in recent years. Hearables are considered one of the most likely candidates to replace smartphones. A variety of services have been proposed that are possible only with hearables3).
3.1 Listening to the future: how hearables can change our world
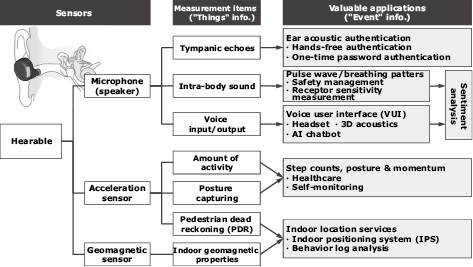
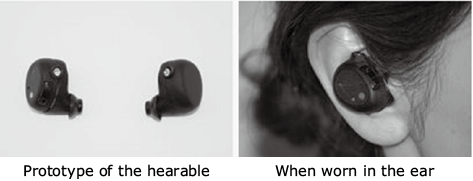
In the near future, people will increasingly find themselves working closely with AI systems and robots. Hearables provide a powerful and convenient interface that will seamlessly integrate people, “things”, and AI without interfering with people’s ability to conduct activities in physical space4)5). The functions of the hearable now being developed by NEC are listed in Fig. 3, while the photos show what it will look like. This device is equipped with a microphone, speaker, motion sensor, and geomagnetic sensor. The microphone and speaker make it possible to perform individual authentication using ear acoustic authentication and vital sensing using intra-body sound while providing a voice user interface (VUI). The motion sensor enables the wearer’s activity and posture to be tracked, while the geomagnetic sensor makes it possible to track indoor location. A single device is able to specify who, where, and in what condition is unprecedented. In collaboration with various partners, NEC is now conducting verification tests for implementation of this device6).
3.2 Usage scenarios
There is a wide range of possible applications for hearables. Fig. 4 shows some of the usage scenarios.
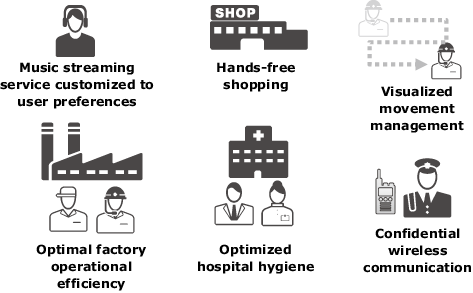
The first example is a music streaming service. When the users wear a hearable, they can be authenticated without having to remember passwords or usernames, while the service automatically caters to their preferences. Continuous user authentication ensures that only the authorized user is using the service, enabling the service provider to provide continuous service without worrying about unauthorized use.
With hearables, shopping becomes more convenient than ever. Users can pick and choose items to purchase without holding anything in their hands — with no need to pull out a credit card or smartphone — because authentication can be performed with ear acoustic authentication.
Hearables can also be used to manage the movement of workers, enabling accurate visualization of which worker is working where. This provides analysis data that can be used to help improve operational efficiency, while preventing fraudulence in duties and assignments.
Now let’s turn our eye to factories and hospitals. The ear acoustic authentication technology makes it possible to perform authentication even when users are wearing gloves and masks. This ensures optimal operational efficiency because authentication can be performed without requiring removal of gloves and masks. Another beneficial aspect of this technology is enhanced hygiene and cleanliness.
Our last example is wireless communication between security guards. By using ear acoustic authentication to ensure that only legitimate personnel are wearing the device, communication with high confidentiality can be assured. Moreover, instead of simultaneously transmitting one user’s voice to all users — as happens in the transceiver mode conventionally used in this field, ear acoustic authentication makes it easy to control communications so that the voice is transmitted only to a specific user or group.
4. Conclusion
In this paper we have reviewed the technology of ear acoustic authentication — how it works and how it can be used. Ear acoustic authentication offers the capability to achieve high security in a non-intrusive hands-free, eyes-free manner that does not interfere with users’ actions or make them aware that they are being authenticated. Through the development of biometric technologies and their application in the real world, NEC is committed to helping make possible a safe, secure, efficient, and equal society where everyone can live a life of abundance.
Reference
- 1)
- 2)
- 3)Nozawa, Uno, “Mimi no Nakani Computer Hearable ga Sekai wo Kaeru,” Nikkei Electronics, 2017.6, PP.23 (in Japanese)
- 4)
- 5)
- 6)
Authors' Profiles
Principal Researcher
Biometrics Research Laboratories