Global Site
Breadcrumb navigation
Security Governance in Secure Development
NEC Security BlogSep 19, 2025
Security governance is a key element for determining an organization's overall security policies and strategies and reducing risks. This blog introduces practices and tips for security departments to implement secure development, based on the framework and objectives of security governance defined in ISO/IEC 27014 (Information Security Governance), with examples from NEC.
Table of Contents
What is Security Governance?
The environment surrounding security is becoming increasingly complex year by year, with factors such as the increasing sophistication of cyberattacks, the strengthening of laws and regulations, and the growing visibility of supply chain risks. Under these circumstances, the importance of security governance—establishing organization-wide security policies and strategies to reduce risks—is growing significantly.
According to ISO/IEC 27014 (Governance of Information Security), “security governance” can be understood as the process by which an organization establishes security objectives and strategies aligned with its operational goals and strategy, implements activities based on these, and continuously evaluates and analyzes them. (Note: While ISO/IEC 27014 terms it “Information Security Governance,” as it is applicable beyond information security, it is simply referred to as “Security Governance” in this blog.) The primary purpose is for senior management to lead in defining the strategic direction for security and to work toward its realization across the entire organization.
On the other hand, there is a similar term “security management” which refers to the execution at operational teams within the framework of security governance. An Information Security Management System (ISMS) based on ISO/IEC 27001 is a management system designed to maintain confidentiality, integrity, and availability of information assets. It consists of a continuous process based on the PDCA cycle, including risk assessment, implementation of countermeasures, operation, and improvement.
Considering security governance and security management in terms of objectives, subject, and expected results, the differences are as follows. (Compiled by the author based on ISO/IEC 27001 and ISO/IEC 27014)
| Item | Security Governance | Security Management |
|---|---|---|
| Objective |
|
|
| Subject | Management and Administrative Departments | Operational Departments (Managers/Employees) |
| Expected Results |
|
|
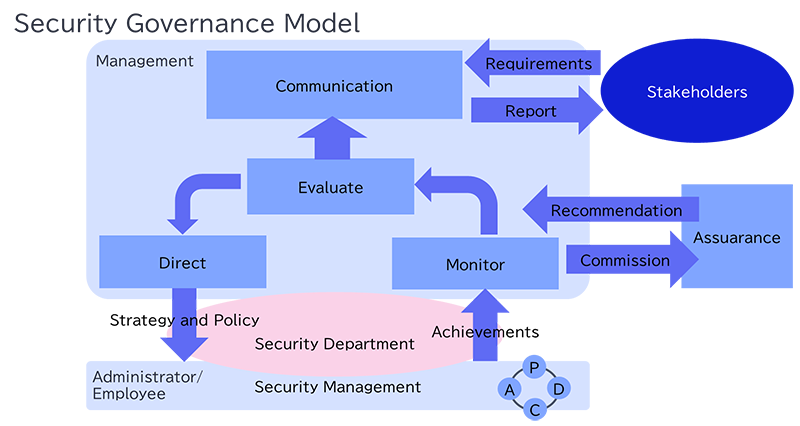
Also, the relationship between security governance and security management is as shown in Figure 1. Governance determines “what to protect and to what extent,” while management implements “how to protect it.”
The Relationship between Secure Development and Security Governance
NEC's secure development practices for products, systems, and services are based on the Security by Design  [1] concept, defined by the former Cabinet Cyber Security Center (now the National Cyber Coordination Office) as “measures to ensure information security from the planning and design stages.” This approach considers security from the planning and design stages to minimize backtracking and reduce costs.
[1] concept, defined by the former Cabinet Cyber Security Center (now the National Cyber Coordination Office) as “measures to ensure information security from the planning and design stages.” This approach considers security from the planning and design stages to minimize backtracking and reduce costs.
Security governance is essential to ensure secure development is practiced effectively in operational teams, rather than relying on an ad hoc approach dependent on individual engineers' efforts. NEC has established its Cybersecurity Management Regulations as a company-wide policy effective from 2023 to define secure development structures and processes within each organization, serving as an expression of its security governance strategy and policies.
Establishing the Structures and Processes Supporting Secure Development Governance
In this chapter, we explain how NEC practices secure development governance, referencing the security governance model outlined in ISO/IEC 27014.
Processes Necessary for Practicing Security Governance
ISO/IEC 27014 lists the following five processes as necessary for practicing security governance.
| Process | Explanation (summarized by the author) |
|---|---|
| Evaluate | Management considers the current status and future projections regarding security objectives and strategies, and makes necessary adjustments to optimize their achievement going forward. |
| Direct | Management presents the company's security objectives and strategy to administrators and employees |
| Monitor | Management visualizes and monitors the status of governance activities to assess the achievement of security objectives and strategy |
| Communicate | Management and external stakeholders exchange security-related information necessary for both parties |
| Assure | Management outsources independent, objective audits, reviews, and certifications to external parties |
These are processes implemented by management, but since it is difficult for management to conduct them on their own, many companies likely have a security department that creates the foundation for executing these processes and serves as a bridge between management and operational teams managers and employees. As shown in Figure 1, the security department primarily handles the “Direct” and “Monitor” aspects.
Regarding these two processes, NEC's security department breaks them down and implements them as follows:
- Security Policy Formulation and Maintenance: Establishing security policies and regulations that reflect management's intent
- Structure Development: Assigning responsible parties and promoters, clarifying role divisions
- Process Design: Standardizing the flow of risk assessment, countermeasure implementation, auditing, and improvement
- Operational Support: Developing standards and guidelines considering implementation feasibility, plus operational support
- Monitoring and Improvement: Assessing status and proposing improvements through self-checks and audits
Practicing Security Governance in NEC's Secure Development
In NEC's secure development, the Security Department practices security governance and supports security management in the operational environment through measures such as the following.
- Security Policy Formulation and Maintenance
The “Cybersecurity Management Rules” have been established as a security policy reflecting management's intent. This policy requires all organizations to build the necessary structures and processes to enhance the security of the products, systems, and services provided to customers. - Structure Development
The previously mentioned cybersecurity management rules outline the assignment of security officers and their roles to promote secure development within the company. Security officers are assigned to all business divisions, and they utilize meetings and communities to coordinate with the security department and each business division. - Process Design
The secure development process is standardized by cybersecurity implementation standards established with reference to external benchmarks such as ISO/IEC 15408, ISO/IEC 27001, and NIST SP 800-53. Also, for each product, system, and service developed and operated, checklists are prepared to verify that countermeasures aligned with standards are implemented. A system has been developed and introduced that provides centralized management of the implementation status. Initial response procedures and report formats for incident occurrences are also established, enabling rapid response and building an improvement cycle aimed at preventing recurrence. - Operational Support
To implement security measures at operational teams, manuals for countermeasures by elemental technology and guidelines for countermeasures against the latest technologies are issued and maintained. During manual revisions, feedback from operational teams is incorporated. - Monitoring and Improvement
Each organization's compliance with cybersecurity management regulations is monitored by the security department through self-checks and audit procedures. This enables the identification and corrective guidance of organizations with deficiencies, aiming to maintain compliance across all organizations.
For more information, including the above content, please refer to NEC's “Cybersecurity Management Report” [2], which summarizes our activities related to security governance and secure development.
Key Points for Designing and Operating Policies and Standards
ISO/IEC 27014 defines the following six objectives for security governance. These are also useful for designing and operating policies and standards. Below is a summary of the six objectives based on my understanding.
- Establish Comprehensive Security throughout the Entire Organization
It is important for security activities to be carried out as a unified effort throughout the entire organization.
Decision-making must be conducted by the entire organization, considering all aspects of the business and related matters.
Furthermore, while the responsibility for implementing security measures and the accountability for the results of those measures must cover the full scope of the organization's activities, the storage and transfer of information by external third parties can extend this responsibility beyond the organization's boundaries. - Make Decisions Based on Risks
Security governance should be decisions made based on risk, and the level of security required should ideally be determined based on what the organization considers to be risks (such as compliance risks, loss of competitive advantage, business interruption, loss of credibility, financial damage, etc.). Furthermore, risk management should be integrated with the organization's overall risk control, and the necessary resources should ideally be allocated by management. - Set Direction to Optimize Investments
It is important to establish a security investment strategy based on business outcomes, balance short-term and long-term business and security requirements, and meet stakeholder needs. Management should integrate security-related processes with existing organizational processes (capital and operating expenditures, compliance, risk reporting) to optimize security investments. - Ensure Alignment with Internal and External Requirements
It is important to ensure policies and practices comply with laws, contracts, and internal and external requirements. To guarantee this compliance, it is desirable for management to commission independent security audits. - Foster a Positive Security Culture
Security governance should incorporate the needs of all stakeholders based on organizational culture. This is because human behavior is one of the fundamental elements supporting an appropriate level of security. Without proper harmonization, discrepancies in objectives and roles among stakeholders may arise and lead to failure in achieving business goals. Thus, alignment and consensus among stakeholders are important. Management should maintain policy consistency and promote and support education, training, and awareness to foster a security culture. - Review the Performance of Security Controls and Link Them to the Business
Security governance must ensure that security controls support the organization and align with the objective of maintaining the security level agreed upon within the organization. Management should evaluate the performance of security controls, including not only their effectiveness and efficiency but also their impact on the business. It is desirable to align this performance with business outcomes through monitoring and auditing.
Given the points above, I believe the following are key tips for enhancing the effectiveness of security governance from the perspective of the security department.
- Unifying Strategy and Policy
- It is important to establish regulations and standards that align with the business risks prioritized by management. This ensures greater consistency in internal initiatives. At NEC, management has determined that inadequate security measures constitute a business risk in recent incidents. Therefore, secure development rules—including regulations and standards—have been standardized company-wide, and we are rigorously implementing a policy to apply secure development to all products, systems, and services provided to customers.
- Furthermore, communications from senior management directly to the entire company regarding these strategies and policies are expected to deepen understanding at operational teams. At NEC, executives participate in biweekly meetings for security officers and deliver messages through internal blogs and other channels.
- Establishing Execution Processes and Systems
- Even with regulations and standards, governance cannot be achieved without processes and structures in place to implement them at operational teams. However, since establishing a perfect system from the beginning is difficult, it is preferable to develop it incrementally by setting stages and defining scopes. At NEC, in addition to developing checklists to confirm the implementation of security measures aligned with standards, we have been developing and deploying new tools since around 2019 to enhance operational efficiency. These include hardening automation tools and vulnerability assessment tools. Going forward, we plan to explore the development and deployment of AI-based tools to assist with secure development.
- It is also crucial that the rules and structures align with the operational realities at operational teams. It is important to find compromises through dialogue between what the security department wants to implement and what operational teams can actually practice. However, if compromises involve creating too many exceptions or case-by-case rules, it can become overly complex, ultimately leading to uncertainty about what should actually be implemented. Therefore, the key is to keep things as simple as possible.
- Fostering a Security Culture
- To ensure processes and structures are followed, it is essential to carefully explain their background and build consensus. Since the Ministry of Economy, Trade and Industry issued the “Cybersecurity Management Guidelines”
 [3], the concept that “inadequate security measures represent a business risk” has become widespread. With numerous real-world incidents where cyberattacks have caused damages severe enough to threaten business operations, both operational teams and management have significantly shifted their awareness. Building a culture where security is considered a matter of course takes time. However, taking advantage of the situation as a tailwind, creating more opportunities for operational teams to think about security through training and events, sharing case studies to help them understand it's not someone else's problem, and continuing these efforts will lead to the cultivation of such a culture.
[3], the concept that “inadequate security measures represent a business risk” has become widespread. With numerous real-world incidents where cyberattacks have caused damages severe enough to threaten business operations, both operational teams and management have significantly shifted their awareness. Building a culture where security is considered a matter of course takes time. However, taking advantage of the situation as a tailwind, creating more opportunities for operational teams to think about security through training and events, sharing case studies to help them understand it's not someone else's problem, and continuing these efforts will lead to the cultivation of such a culture.
- To ensure processes and structures are followed, it is essential to carefully explain their background and build consensus. Since the Ministry of Economy, Trade and Industry issued the “Cybersecurity Management Guidelines”
There are still many aspects we need to improve and many things we must address going forward, but I have summarized the key points by looking back on our progress as of this point.
Summary
I believe security governance in secure development is a structure for the entire organization to “think, execute, and improve” security. The security department, guided by executive leadership, establishes the frameworks and standards that enable operational teams to implement security practices. They are responsible for continuously supporting and improving these efforts. Security is not just about “protecting” – it can become a strategic element for “building trust.” Being in the position of establishing the foundational policies and standards for this is truly a sobering responsibility. I sincerely hope this article provides some useful insights to others in similar roles.
References
- [1]情報セキュリティを企画・設計段階から確保するための方策 (SBD(Security by Design))
 https://www.nisc.go.jp/pdf/policy/general/SBD_overview.pdf
https://www.nisc.go.jp/pdf/policy/general/SBD_overview.pdf - [2]サイバーセキュリティ経営報告書2025
https://jpn.nec.com/sustainability/ja/security/index.html - [3]サイバーセキュリティ経営ガイドライン
 https://www.meti.go.jp/policy/netsecurity/mng_guide.html
https://www.meti.go.jp/policy/netsecurity/mng_guide.html
Profile
Atsuko Imose, CISSP, RISS
Responsibilitiy Area: Security Implementation Technology
Specialization: Security Implementation Technology
Engaged in NEC's security proposal and implementation promotion through developing OS/middleware fortification tools, conducting risk assessments, and supporting security requirement definition and design. Currently primarily responsible for establishing regulations and guidelines for security implementation. Holds CISSP, CISA, and Information Security Support Specialist (RISS) certifications.
Hobbies include weekend yoga and occasional handmade crafts (making plum wine, plum syrup, miso, jam, etc.)—a mother engineer.
